Underwater robotics has emerged as a transformative era in marine exploration and research, allowing scientists, engineers, and explorers to delve deeper into the mysteries of the ocean with extraordinary precision and efficiency.
![[GetPaidStock.com]-65e0459756753 [GetPaidStock.com]-65e0459756753](https://geres-asso.org/wp-content/uploads/elementor/thumbs/GetPaidStock.com-65e0459756753-qkko94m53kye5l2vuh5a8fw4rb35tpulckajuwkbp4.jpg)
This article explores the pivotal position of underwater robotics in advancing our knowledge of the marine environment, from mapping uncharted depths to studying elusive marine lifestyles and uncovering hidden treasures underneath the ocean.

Underwater robots, additionally referred to as remotely operated vehicles (ROVs) and self sufficient underwater automobiles (AUVs), play a important role in exploring the sizeable and uncharted depths of the sea.

Underwater robotics gives scientists with unprecedented access to marine ecosystems and flora and fauna habitats, making an allowance for the take a look at and commentary of marine existence in their herbal environment.
Underwater robotics plays a vital function in monitoring the health and situation of the world’s oceans, which include tracking changes in water first-class, temperature, and acidity. ROVs and AUVs equipped with environmental sensors can acquire actual-time data on oceanographic parameters, allowing scientists to reveal and reply to environmental threats inclusive of pollution, coral bleaching, and ocean acidification.
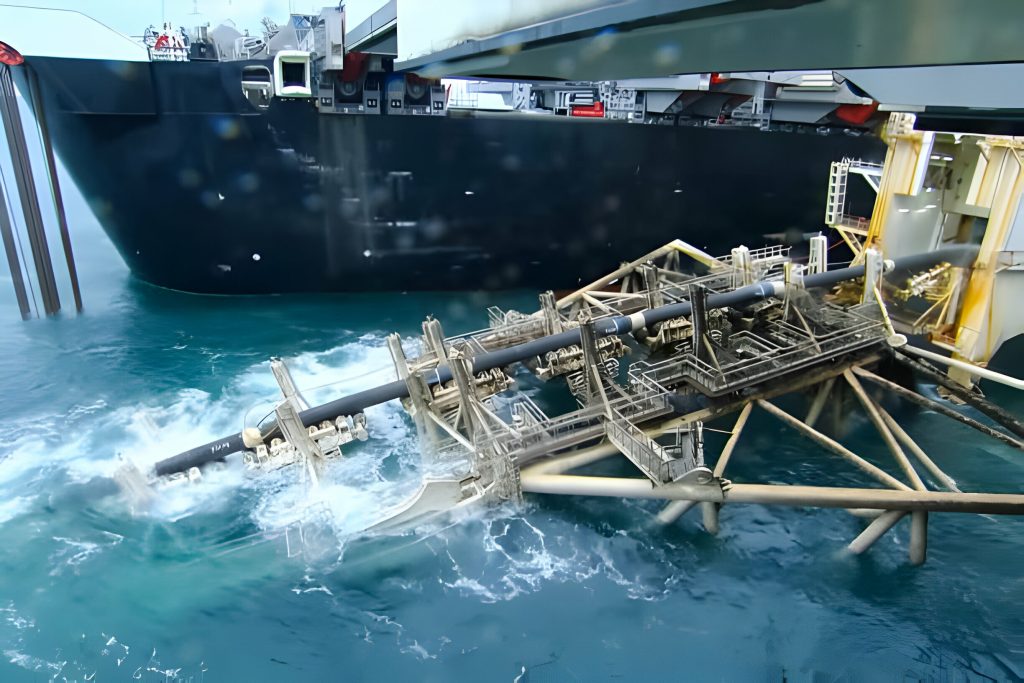
Underwater robotics permits high-resolution mapping and surveying of underwater terrain, which includes the mapping of underwater topography, geological features, and archaeological web sites. ROVs and AUVs prepared with superior sonar and imaging structures can create precise 3D maps of underwater landscapes, supplying valuable insights into the geology, morphology, and evolution of the sea floor.

Underwater robotics plays a important position in seek and rescue operations, imparting first responders with the equipment and competencies to discover and get better items or people lost at sea. ROVs ready with cameras, lights, and manipulator palms can search underwater wreckage, behavior underwater inspections, and help inside the retrieval of submerged objects or sufferers in hard underwater environments.
